The Privacy Amendment (Notifiable Data Breaches) Act 2017 established the Notifiable Data Breaches (NDB) scheme that came into effect in Australia on February 22nd 2018. You need to be more prepared than ever before.
This new layer of protection for personal data applies to government agencies, private sector organisations with annual turnovers of over AU$3M, and other organisations handling health information or involved in credit reporting. According to the amendment, an eligible data breach now encompasses unauthorised access to or unauthorised disclosure of personal information, and that in the case of a breach, qualifying organisations will be required to notify the Australian Information Commissioner (OAIC) and the victims of the breach as they promptly investigate the matter within 30 days.
Failure to comply will attract heavy fines.
Organisations need to prepare to reduce the risk of data breach, and to set up a data breach response plan that includes the required notifications. While we advise you seek your own legal advice to ensure compliance, we have prepared a 10-point checklist below to help you ready your team and organisation if you have not already done so.
Tip1. Understand the data your organisation has and where it resides
It seems obvious. However, you'd be surprised how much data is floating around inside organisations in spreadsheets and exposed online databases. You need to determine the scale and type of records that could be compromised and all the individuals that belong to it. Assess the level of sensitivity in the data and the susceptibility to abuse. Also, consider any external parties through which this data might flow and ensure they take privacy as seriously as you do.
Tip 2. Audit access rights
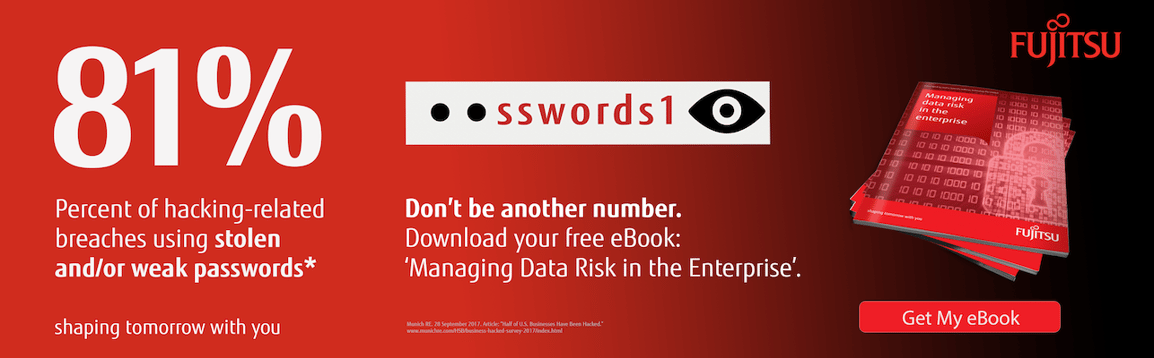
People come and go. Access must be aligned to their needs while working with you - and removed when they leave. No matter which database management system you use for your data storage, you need to manage the access to that system and the data they can see. Be sure all users continually update passwords, and that they understand your expectations when it comes to sharing access, leaving their computers unattended, and how to manage their mobile devices in cafes and other public spaces.

Tip 3. Conduct system audit trails
Should a data breach occur, your systems need to be in a position to reveal who accessed what and at what time. Such audit trails can come in handy to assess the extent of the breach (important for your notification obligations) as well as proving to regulators that the violation was contained early enough before any significant damage occurred.
Tip 4. Have a data breach response plan and run simulations against it
A good data breach response plan will adapt to the specifics of any individual data breach. It needs to contain team member names, communication channels (both internal and external), the role of each team member, a snapshot of the location of the data, and how systems can be shut down quickly.
Consider a simulation. Just like a test evacuation in case of a fire, a test data breach simulation can help you produce a refined response and identify potential gaps. You can engage the services of white-hat hackers or run penetration testing services to test the response you would instigate in the case of a real breach. You cannot be too prepared.
Tip 5. Create a data breach response team
You need to have a small and well-skilled response team that can take action under pressure should a breach occur. These can be internal, external, or a combination of both to ensure 24/7 readiness. Ensure all staff are aware of the response personnel and have dedicated lines for reporting suspected data breaches to the team. Your emergency response team should be in a position to know which stakeholders to contact immediately depending on the type of breach. Insist on the team recording every data breach no matter how minor. Also, consider appointing a second point of contact for every member of the response team in case if vacation or sick leave.
Tip 6. Have current and adequate data insurance
Never assume the cyber insurance policy you have will be enough to mitigate all types of losses in your organisation. Check to be sure you have this type of insurance for data, and then ensure it is comprehensive enough for the kind of business, technology and processes you operate.
Tip 7. Update your 3rd party arrangements and processes inside your data supply chain
It's important to make a serious attempt to implement the right processes and 3rd party arrangements inside your data supply and management chain in order to both minimise the chance of a data breach, and then ensure the right action in the case of a data breach. Enforce contractual agreements with your contractors and subcontractors that will enable you to audit their systems and processes regularly too.
Tip 8. Update the technology inside your data supply chain.
Deploying the right technology can reduce the risk of a data breach. This includes the database management system you deploy, the data storage strategy you run with, and specific technologies such as data masking and encryption features (found inside FUJITSU Enterprise Postgres).
Tip 9. Stay updated with guidance and information issued by the OAIC
You can find a range of resources on the OAIC website including guides and training materials for various industries. Keep yourself, and your organisation, up-to-date with any new information as the regime begins to establish itself, and you deploy your new processes and technologies.
You can see the 1st quarter report here.
Tip 10. Secure hard copies of essential documents
Some data breaches are so fatal they lock out administrators or freeze online records, making it impossible to access notes or plans in the system. Old-fashioned as it may be, with this regime in place, you might want to keep physical copies of critical documents such as your data breach response plan handy for reference following an attack.
A final word
More than ever, protecting your organisation against potential data breach is now a significant priority. A minor data breach can lead to severe consequences including substantial fines, damage to your brand, and even an inability to obtain data insurance. So make sure you take these steps and more to give yourself every chance of protection - and then compliance should a data breach occur in our ever more compliance-driven world.
If you have data security concerns and you are looking for a more robust, secure and scalable database, then contact one of our experts on +612 9452 9191. You may also wish to consider migrating to our PostgreSQL-based FUJITSU Enterprise PostgreSQL product for key security features and total cost of ownership up to 80% or more lower than traditional proprietary-based systems.