It is no longer just banks and governments, but all companies who are required to protect their own data as well as their customers' in order to comply with privacy legislation such as the European Union’s GDPR. The need to protect their data is also caused by malicious hackers trying to piece together information so they can impersonate someone’s identity, for either financial gain or to hide their own identity.
While storage devices and file systems can provide a level of encryption for data stored on them, for databases the problem is much larger than a single installation. It must be easily applied no matter where the databases tables or logs are placed or copied, and in such a way that the data is secure and easily recovered in case of failure or disaster recovery scenarios.
Anticipating this, Fujitsu Enterprise Postgres has implemented Transparent Data Encryption (TDE), which securely stores individual tablespaces and logs encrypted with their own encryption keys, ensuring security of user data while preserving ease of management for database administrators.
PCI DSS-compliant 256-bit encryption, out of the box
Unlike other proprietary databases, you do not have to purchase additional products or modules to apply the highest level of security to your data. We provide Transparent Data Encryption free of charge, so your business complies with PCI DSS requirements.
Unlike PostgreSQL's pgcrypto module (more on this next week), the native TDE functionality does not require existing applications to be modified.
Leveraging Intel hardware encryption acceleration, the impact of encrypting and decrypting the data is minimised so that high performance applications can easily have their data secured with minimal overhead.
A vital extra layer of security
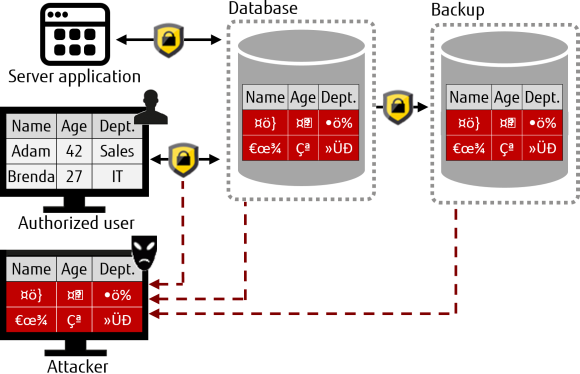
A database is protected from unauthorised access by registering users and making them go through authentication and access controls. However, this does not protect the underlying operating system files from attackers, who can bypass the database server's authentication and access controls.
With Fujitsu Enterprise Postgres, data in the operating system files is encrypted by the TDE feature, so that valuable information is protected even if the file or disk is stolen. Data stored in the database is encrypted at write time, and decrypted during read. This is performed automatically by the instance, so neither the users nor the applications need to be concerned with key management or encryption/decryption.
What is the data scope for transparent data encryption?
The following is automatically encrypted using TDE:
- Tablespaces
All data within specified tablespaces — tables, indexes, temporary tables, and temporary indexes. - Backup data
Backups of encrypted data will also be encrypted. - WAL
WAL, which is created by updating encrypted tables and indexes, is encrypted with the same security strength as the update target. - Temporary files
When large merges and sorts are performed, the encrypted data is written to a temporary file in encrypted format. - Streaming replication support
You can combine streaming replication and transparent data encryption — data and WAL encrypted on the primary server will be transferred to the standby server in its encrypted format and stored.
Key attributes
- Encryption key can be changed without having to re-encrypt data
- No need to modify existing business applications for migration
- Compliant with Payment Card Industry Data Security Standard (PCI DSS)
- Encryption key and data are managed separately
- Encryption key can be replaced regularly
- Confidential information can be made unrecognisable
- 256-bit encryption
- Storage data security utilising Advanced Encryption Standard (AES) — the latest security standard



