
The security of databases is of paramount importance for an organization’s reputation. Modern databases handle a massive workload of sensitive information and must have robust security safeguards in place. This is where the design principles outlined by Federal Information Processing Standards (FIPS) come into play.
What is FIPS 140-2?

FIPS 140-2 is a standard developed by the National Institute of Standards and Technology (NIST) that defines the requirements for cryptographic modules used in securing sensitive information. By adhering to these standards, modern databases can ensure that they have implemented the necessary security measures to protect against unauthorized access, data breaches, and other cyber threats. These safeguards are critical in safeguarding the integrity, confidentiality, and availability of the data stored within the database, ultimately providing peace of mind for organizations and their stakeholders.
Why should my database be FIPS-compliant?

By achieving FIPS compliance, organizations are able to demonstrate they have undergone the demanding testing that is required to meet the necessary standards. The validation process is voluntary, but many organizations require that cryptographic modules used in their systems be validated to FIPS 140-2.
Who enforces compliance with FIPS?

The validation process involves testing the cryptographic module against the standard’s requirements and then submitting the test results to the CMVP for review and certification. Once a cryptographic module is validated, it is added to the list of validated cryptographic modules maintained by NIST.
Fujitsu Enterprise Postgres extends PostgreSQL security features
Fujitsu takes PostgreSQL security to new heights with Fujitsu Enterprise Postgres. This enterprise-grade database solution adds an extra layer of protection to PostgreSQL's already robust security features, ensuring unparalleled data security for businesses.
Transparent Data Encryption - 256-bit encryption is one of the most secure encryption methods available as it uses a 256-bit key to encrypt/decrypt data. Our built-in encryption feature automatically encrypts tablespaces, without the need to modify existing applications.











Policy-based password management - Prevent unauthorized logins and improve database security with the ability to restrict logon and manage the password complexity, number of consecutive failures, and password expiry date.


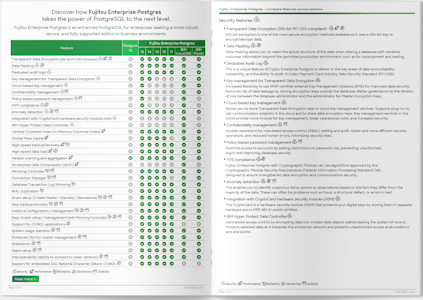
To explore the full range of enhancements that Fujitsu Enterprise Postgres brings to PostgreSQL's exceptional performance, reliability, and security capabilities, download our brochure 'Compare features across versions'.

The bottom line
 Fujitsu continues to demonstrate its commitment to excellence by completing the FIPS 140-2 validation program and acquiring our certificate (#4658). Fujitsu Enterprise Postgres is now eligible to be procured by U.S. federal agencies, including the Department of Defense, as well as for use in regulated industries such as utilities, finance, and healthcare.
Fujitsu continues to demonstrate its commitment to excellence by completing the FIPS 140-2 validation program and acquiring our certificate (#4658). Fujitsu Enterprise Postgres is now eligible to be procured by U.S. federal agencies, including the Department of Defense, as well as for use in regulated industries such as utilities, finance, and healthcare.
Take it for a spin and see for yourself
You can try Fujitsu Enterprise Postgres with a fully-featured trial version to experience a frictionless hybrid cloud that can help you modernize to respond faster to business demands. Contact us to obtain your trial version.


 Fujitsu has partnered with SafeLogic to equip Fujitsu Enterprise Postgres with a FIPS-compliant crypto library that protects your data at rest and data in flight through robust cryptographic algorithms.
Fujitsu has partnered with SafeLogic to equip Fujitsu Enterprise Postgres with a FIPS-compliant crypto library that protects your data at rest and data in flight through robust cryptographic algorithms.


 PostgreSQL Insider
PostgreSQL Insider 
